AI Data Breaches: Why They Happen and How to Protect Your Business
Artificial intelligence (AI) is rapidly transforming industries. It offers businesses innovative solutions and automation capabilities. But with this progress comes a growing concern: AI data breaches. As AI becomes more integrated into our systems, the risks increase. The data it collects, analyzes, and utilizes becomes a target.
A recent study on AI security breaches revealed a sobering truth. In the last year, 77% of businesses have experienced a breach of their AI. This poses a significant threat to organizations. A breach can potentially expose sensitive data, compromise intellectual property, and disrupt critical operations.
Why AI Data Breaches are Growing in Frequency
Several factors contribute to the increasing risk of AI data breaches:
- The Expanding Attack Surface: AI adoption is increasing fast. As it increases, so does the number of potential entry points for attackers. Hackers can target vulnerabilities in AI models and data pipelines, as well as the underlying infrastructure supporting them.
- Data, the Fuel of AI: AI thrives on data. The vast amount of data collected for training and operation makes it a tempting target. This data could include customer information, business secrets, and financial records. And even personal details of employees.
- The “Black Box” Problem: Many AI models are complex, making identifying vulnerabilities and tracking data flow difficult. This lack of transparency also makes it challenging to detect and prevent security breaches.
- Evolving Attack Techniques: Cybercriminals are constantly developing new methods to exploit security gaps. Techniques like adversarial attacks can manipulate AI models. This can produce incorrect outputs or leak sensitive data.
The Potential Impact of AI Data Breaches
The consequences of an AI data breach can be far-reaching:
- Financial Losses: Data breaches can lead to hefty fines, lawsuits, and reputational damage. This can impact your bottom line significantly.
- Disrupted Operations: AI-powered systems are often critical to business functions. A breach can disrupt these functionalities, hindering productivity and customer service.
- Intellectual Property Theft: AI models themselves can be considered intellectual property. A breach could expose your proprietary AI models, giving competitors a significant advantage.
- Privacy Concerns: AI data breaches can compromise sensitive customer and employee information. This can raise privacy concerns and potentially lead to regulatory action.
Protecting Your Company from AI Data Breaches: A Proactive Approach
The good news is that you can take steps to mitigate the risk of AI data breaches. Here are some proactive measures to consider.
Data Governance
Put in place robust data governance practices. This includes:
- Classifying and labeling data based on sensitivity
- Establishing clear access controls
- Regularly monitoring data usage
Security by Design
Integrate security considerations into AI development or adoption. Standard procedures for AI projects should be:
- Secure coding practices
- Vulnerability assessments
- Penetration testing
Employee Training
Educate your employees about AI security threats and best practices for data handling. Empower them to identify and report suspicious activity.
Security Patch Management
Keep all AI software and hardware components updated with the latest security patches. Outdated systems are vulnerable to known exploits, leaving your data at risk.
Stay Informed
Keep yourself updated on the latest AI security threats and best practices. You can do this by:
- Subscribing to reliable cybersecurity publications
- Attending industry conferences
- Seeking out online workshops on AI and security
Get Help Building a Fortress Against AI Data Breaches
AI offers immense benefits. However, neglecting its security risks can leave your company exposed. Do you need a trusted partner to help address AI cybersecurity?
Yeo & Yeo Technology’s team will examine your entire IT infrastructure, including AI and non-AI components. We’ll then help you implement proactive monitoring and protection measures. Contact us today to schedule a chat about your cybersecurity.
The article is used with permission from The Technology Press.
Robotic Process Automation is a technology that uses software robots or “bots” to automate repetitive, rule-based tasks typically performed by humans. These bots can interact with digital systems and software just like a human user but with greater speed, accuracy, and consistency.
It’s important to clarify that Robotic Process Automation does not aim to replace human workers; rather, it complements and enhances their capabilities. By automating mundane and repetitive tasks, RPA frees up employees to focus on more strategic, creative, and complex activities that require human insight and decision-making.
Key Benefits of RPA
- Increased Efficiency: RPA bots can work 24/7 without breaks, significantly reducing the time required to complete tasks.
- Improved Accuracy: RPA ensures higher accuracy in data entry and other repetitive tasks by eliminating human error.
- Cost Savings: Automating routine tasks allows businesses to reallocate human resources to more strategic, value-added activities.
- Enhanced Customer Experience: Faster processing times and fewer errors lead to improved customer satisfaction.
Applications of RPA in Business
RPA can be applied across various business functions:
- Finance and Accounting: Automating invoice processing, reconciliations, and report generation.
- Human Resources: Streamlining onboarding processes, payroll management, and employee data updates.
- Customer Service: Handling routine customer inquiries and processing simple requests.
- IT Operations: Automating system monitoring, user account management, and software installations.
Implementing RPA in Your Business
While the benefits of RPA are clear, implementing it effectively requires careful planning and expertise. It’s crucial to identify the right processes for automation, choose the appropriate RPA tools, and ensure seamless integration with existing systems.
At Yeo & Yeo Technology, we understand the challenges businesses face in adopting new technologies. Our dedicated Business Applications Group specializes in helping companies like yours harness the power of RPA to drive efficiency and growth. Whether you’re looking to automate a single process or transform your entire operation, our team can guide you through every step of the RPA journey.
What are some of the key differentiators that can propel businesses forward? They include efficiency, productivity, and innovation. Microsoft has expanded the availability of one of its most dynamic tools to SMBs. A tool that can be a real game-changer for growth.
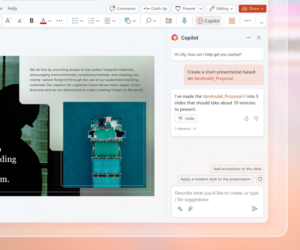
Copilot for Microsoft 365 is a powerful new addition to the M365 suite. It was first offered to enterprise customers only. However, Copilot is now open to businesses of all sizes, as long as they have Microsoft 365 Business Standard or Business Premium accounts. Microsoft has positioned Copilot to revolutionize the way SMBs work. This innovative AI tool empowers users to generate creative content. It also streamlines workflows and unlocks new levels of productivity.
How Copilot Streamlines Workflows
Copilot leverages the power of large language models (LLMs). LLMs are AI models trained on massive datasets. This enables Copilot to understand natural language and generate contextual responses. It offers intelligent suggestions and content within your Microsoft 365 applications.
Here’s how Copilot translates this technology into real-world benefits for your business:
Effortless Content Creation
Struggling with writer’s block or repetitive tasks like email writing? Copilot can suggest text responses and complete sentences. It can even draft entire emails based on your initial input.
With just a few guiding prompts, your team can:
- Craft compelling marketing copy
- Write concise customer service responses
- Create dynamic PowerPoint presentations
Enhanced Productivity
Copilot automates repetitive tasks and streamlines workflows by offering intelligent suggestions. This can free up valuable time for your employees. It allows them to focus on more strategic initiatives, high-value projects or core business activities. Imagine automatically generating reports or automating data entry tasks. This unleashes your team’s energy for creative problem-solving and innovation.
Improved Communication and Collaboration
Clear and concise communication is vital for any successful business. Copilot facilitates this by doing things like:
- Suggesting relevant phrases
- Correcting grammatical errors
- Ensuring consistent messaging across different applications
Improved communication fosters better collaboration within teams. This can lead to streamlined project execution and enhanced client interactions.
Reduced Learning Curve for New Technologies
Copilot provides context-aware guidance and suggestions. All while you work with your familiar Microsoft 365 applications. This can significantly reduce the learning curve for new employees. It allows them to become proficient in using the full potential of the suite more quickly. Imagine onboarding new team members with ease and empowering them to contribute meaningfully from day one.
Real-World Applications of Copilot within Your SMB
Copilot’s capabilities extend beyond generic productivity enhancements. Here’s a glimpse into how different roles within your SMB can leverage Copilot:
Marketing and Sales Teams
Generate compelling marketing copy for social media campaigns. Craft tailored sales emails with targeted messaging. Develop engaging presentations with Copilot’s creative text suggestions and language model capabilities.
Customer Service Representatives
Respond to customer inquiries with increased efficiency and accuracy. Use Copilot’s AI-powered suggestions to craft clear and concise responses. Imagine resolving customer issues faster and fostering a more positive customer experience.
Project Managers
Develop comprehensive project plans. Automate progress reports with a few text prompts. Collaborate seamlessly with team members using Copilot’s intelligent features. Streamline project management. Ensure everyone is on the same page from conception to completion.
Content Creators
Overcome writer’s block and generate fresh ideas for website copy. Teams can leverage Copilot’s help in brainstorming and content creation in many areas. Imagine producing high-quality content consistently. All while keeping modern audiences engaged and driving brand awareness.
Finance and Accounting Teams
Automate data entry tasks and improve data analysis with Copilot’s intelligent features. Generate reports with prompts for enhanced clarity. Imagine no more struggling to create reports. Gain valuable insights from data faster.
Getting Started with Copilot for Microsoft 365
The good news is that Copilot for Microsoft 365 is readily accessible to SMBs. It integrates seamlessly with your existing environment. Here’s how you can empower your team to leverage this powerful tool:
- Ensure Compatibility: Copilot is currently available for businesses with Microsoft 365 Business Premium or Business Standard accounts.
- Activate Copilot: Buy the Copilot add-on to your subscription. Then, as needed, contact your IT support team for help using it within your Microsoft 365 apps.
- Explore and Experiment: Microsoft Copilot offers intuitive features, all within your familiar Microsoft 365 applications. Start experimenting with its capabilities. Discover how it can enhance your workflow and productivity.
- Invest in Training: Copilot is user-friendly, but you should still consider providing brief training sessions for employees. This helps ensure they understand the tool’s full potential and assists them with leveraging its capabilities effectively.
Improve Your Team’s Use of Microsoft 365
Copilot for Microsoft 365 is not just another software update; it’s a game-changer for businesses. By embracing this innovative AI tool, you can unlock a new level of efficiency and empower your employees to achieve more. Our team can guide you in using this resource to the fullest. Contact us today to learn more.
The article is used with permission from The Technology Press.
Should I let my employees use company apps on their personal phones?
Ideally, no, because you have less control over the security of personal devices. However, threats can be mitigated by using VPNs and multifactor authentication.
Should I ban my team from working in coffee shops because of public Wi-Fi dangers?
You don’t have to. Just ensure they’re aware of the risks of using public Wi-Fi and vigilant when connecting to new networks.
Should we delete phishing emails, or should they be reported?
Any spam or phishing emails should be flagged as such because it teaches your email provider what spam looks like. You can also forward such emails to the Federal Trade Commission at reportphishing@apwg.org.
Information used in this article was provided by our partners at MSP Marketing Edge.
Technology is crucial in maintaining competitiveness and efficiency in today’s fast-paced business environment. However, managing IT infrastructure can be challenging, especially for small and medium-sized businesses. Here are seven signs that indicate your business might benefit from partnering with a Managed Service Provider (MSP):
1. Your IT Team is Overwhelmed
Many small businesses lack a dedicated IT team, and those who do often find their team stretched thin. If your IT staff constantly deals with issues like printer problems, software updates, or cybersecurity threats, it might be time to seek additional support. MSPs provide proactive management and monitoring, allowing your team to focus on their primary responsibilities.
2. Rising IT Costs
As your business grows, so do your IT needs. Hiring skilled IT personnel can be expensive, and managing emerging technologies can strain your budget. MSPs offer cost-effective solutions by providing expert services at a predictable monthly cost, helping you manage expenses more efficiently.
3. Frequent Downtime
Downtime can severely impact your business operations and reputation. If your business experiences frequent outages or technical issues, an MSP can help design a robust IT strategy to minimize disruptions and ensure high system availability.
4. Security Concerns
With the rise of cyberthreats, maintaining robust security measures is essential. If you’re worried about your company’s data security, an MSP can offer advanced security solutions and 24/7 monitoring to protect your systems from potential breaches.
5. Limited IT Staff
Businesses often struggle with understaffed IT departments, leading to inefficiencies and unmet technology needs. MSPs can supplement your existing team, providing the necessary expertise and support to manage your IT infrastructure effectively.
6. Need for Advanced Technology
As technology evolves, businesses must keep up with the latest advancements. If your company struggles to implement new systems or cloud-based solutions, an MSP can guide you through the process, ensuring a smooth transition and optimal use of technology.
7. Strategic Growth Plans
A strategic IT plan is crucial if your business is in growth mode. MSPs can help you develop a technology roadmap that aligns with your business goals, ensuring your IT infrastructure supports your future expansion.
Yeo & Yeo Technology: Your Trusted MSP Partner
Yeo & Yeo Technology offers customized technology solutions tailored to meet the unique needs of your business. Whether you require a full managed service provider or an extension of your current IT team, Yeo & Yeo provides comprehensive services to help you achieve your business objectives. With a focus on proactive management, cost-effective solutions, and advanced security measures, Yeo & Yeo Technology ensures your IT infrastructure is robust, secure, and scalable for future growth.
When small and medium-sized businesses (SMBs) consider cybersecurity threats, the image of a hacker often comes to mind. However, focusing solely on external hackers may overlook other significant threats that can be just as damaging. This article explores why hackers are not the biggest cybersecurity threat and highlights other critical vulnerabilities that SMBs should address.
Internal Threats: The Insider Risk
One of the most overlooked cybersecurity threats comes from within the organization itself. Insider threats can be caused by employees, former employees, contractors, or business associates who have access to critical systems and data. These individuals can unintentionally or maliciously compromise security by mishandling sensitive information or exploiting their access for personal gain.
Weak Passwords and Poor Authentication Practices
Another major vulnerability is the use of weak passwords and inadequate authentication measures. Many SMBs fail to enforce strong password policies or implement multi-factor authentication, leaving them susceptible to unauthorized access. Statistics show that many hacking incidents involve compromised credentials, highlighting the need for robust password management and authentication strategies.
Inadequate Patch Management
Failure to keep software and systems up to date is a common issue that can lead to security breaches. Cybercriminals often exploit known vulnerabilities in outdated software to gain access to networks. SMBs may lack the resources to maintain regular patching schedules, making them attractive targets for attackers. Automated patch management solutions can help mitigate this risk and protect systems against known vulnerabilities.
Ransomware and Malware
While hackers are often behind ransomware attacks, the threat itself is more about the malware and the tactics used to deploy it. Ransomware can harm a business by encrypting critical data and demanding payment for its release. SMBs are particularly vulnerable due to limited resources and often lack the necessary defenses to prevent such attacks. Regular data backups and employee training on recognizing phishing attempts are crucial steps in defending against ransomware.
The Role of SMBs in the Larger Cybersecurity Landscape
SMBs often serve as entry points for attackers targeting larger organizations through supply chain attacks. Cybercriminals may exploit weaker security measures in SMBs to gain access to larger corporate networks. This highlights the importance of SMBs implementing comprehensive cybersecurity strategies not only for their own protection but also to safeguard their business partners.
Yeo & Yeo Technology offers comprehensive solutions tailored to the unique needs of SMBs, including employee training programs, advanced security tools like MFA and firewalls, and guidance on maintaining up-to-date systems. By partnering with YYTECH, you can enhance your cybersecurity defenses and focus on growing your business with confidence. Don’t wait for a breach to occur—take proactive steps today to secure your business’s future.
Data describes everything a business does, from users and clients to services and products. Even the physical locations of warehouses, manufacturing plants, retail stores, and equipment are represented as data. With so much riding on it, the mission to protect this data has become increasingly challenging due to an often hostile online environment.
Hazards in the digital realm have pushed technology and security teams to adopt a zero-trust approach. This means assuming all traffic, regardless of type, location, or origin, is untrustworthy. In a world where assumptions about user identity or location can no longer be made, protecting data without halting business operations is crucial.
The Challenge of Zero Trust in a High-Pace Business Environment
Operating with a zero-trust mindset involves making real-time decisions about the safety of data access requests. This approach is not a single tool or product but a comprehensive strategy that continuously verifies the integrity of every interaction. The fundamental question is: How do we help ensure that the right data is accessed by the right person at the right time? This question must be asked and answered repeatedly to maintain security without disrupting business operations.
Data as the Ultimate Target
Data is a valuable commodity, and cybercriminals will go to great lengths to get their hands on as much of it as they can. Whether it’s an accidental release by an employee or a targeted attack by a malicious actor, data loss can damage a company’s reputation and halt its operations. Traditional security measures, which focused on securing physical locations like offices and networks, are no longer sufficient. Modern businesses operate from various locations and even remotely, making it essential to inspect each data access request in-depth and surround it with robust policies and procedures.
Adapting to a Changing Perimeter
In the cloud-driven world, the technology perimeter has evolved. The focus has shifted from securing pathways to inspecting individual requests for data access. Today’s defenses are built on understanding the user, their recent activities, and the context of their request. This approach forms a new wall of security, helping to ensure that data access is both permissible and reasonable.
Creating a Unified Security Solution
A platform approach with comprehensive insights into data loss prevention, insider risk management, and data protection labeling is necessary to protect data effectively. This approach enables organizations to answer point-in-time access requests with precision. Labels categorize data into critical, essential, confidential, and general information, while data loss prevention controls enforce encryption and other protections. Insider risk management uses machine learning and artificial intelligence to monitor for data exfiltration, often integrating with business context from systems like human resources information systems (HRIS). Retention policies proactively reduce risk by eliminating old, sensitive information.
Building a Foundation of Policies and Procedures
A unified security solution is built on well-documented, shared, and taught policies and procedures. Regular training ensures that end users understand these policies, creating a robust defense mechanism. Interconnected tools and layers of defense enhance the zero-trust framework, making it more difficult for attackers to penetrate and steal data, thus allowing businesses to operate securely.
Assessing Your Zero Trust Adoption
Understanding your organization’s current status in adopting zero trust is crucial. Focusing controls on data and user identity helps create the context needed for quick, risk-informed decisions. Yeo & Yeo Technology, with its security knowledge, assists organizations in identifying their position on the zero-trust path and provides cost-effective actions to help minimize data risks. Contact us to learn more.
Contact Center AI is transforming the way businesses manage customer interactions by automating and enhancing key operations. Instead of replacing human agents, AI acts as an assistant, offering insights and handling routine tasks that do not require human creativity or judgment.
Benefits of Contact Center AI
- Self-Service Capabilities: AI enables customers to manage account features independently and provides basic answers, allowing agents to focus on more complex issues.
- Automated Transcriptions and Summaries: AI records interaction details and updates them across systems like CRM, ERP, and inventory management, streamlining data management.
- Intelligent Call Routing: AI analyzes call reasons and caller details to route customers to the most suitable agents, ensuring quicker and more effective resolutions.
- Performance Insights: AI generates customized reports and insights, helping businesses analyze interactions and improve contact center performance.
Contact Center AI in Action
A call or interaction that solves a unique issue shouldn’t benefit just one customer or agent. An odd challenge a customer is facing could be something that many others are experiencing, not just a one-off situation.
For example, what if a support agent finds out that the problem a customer is having with your product is due to interference from a new feature on another popular app? After discovering the root cause of this issue, you realize you should outline what to do in an article in your online help center. Your contact center AI makes creating and fact-checking the post much more accessible.
First, it has logged and can reference all of the details from the initial customer interaction. Then, generative AI can quickly create an article from that information for a step-by-step solution. All that’s left is for a subject matter expert to review and post the information.
Elevate Your Customer Service with YeoVoice
Yeo & Yeo Technology offers YeoVoice, a cloud phone and contact center solution powered by Elevate, which includes comprehensive AI capabilities. Enhance your customer service experience and drive business success with our innovative technology. Contact us today to learn how YeoVoice can transform your customer interactions.
Information used in this article was provided by our partners at Intermedia.
Protecting your small business from theft is far more complex than it used to be. Gone are the days when locking the doors was enough to minimize the likelihood of intruders. Today, companies face both physical and cyber risks, and it’s critical to understand how they’re intertwined.
The problem with things
Imagine that a thief breaks into one of your employee’s cars and steals a company laptop that contains your entire customer database. Here, physical theft can grant access to digital assets. Among the possibilities are that the crook:
- Is working for a competitor who’s looking for an unfair advantage,
- Will use the customer information to commit identity theft, or
- Might share the data with other criminals on the dark web.
Or consider the risks involved with the Internet of Things. If your business uses smart security devices, such as cameras and door locks, they’re probably connected to the internet. If your cybersecurity defenses are lacking, a criminal could steal your login credentials and disarm your security system, thus gaining physical access to offices and production and storage facilities.
Effective defenses
How then can you prevent physical vulnerabilities from exposing digital assets (and vice versa)? Do the following:
Identify assets. Where do you store your most valuable digital assets? What would happen if they were stolen? Who has access to them? Could thieves easily break in and use the data for nefarious purposes?
Train employees. Make sure employees know how to protect your data and devices with strong passwords and secure practices. They should always employ a virtual private network when using public Wi-Fi and never leave company devices unattended in public. You may also want to prohibit leaving devices in vehicles.
Install mobile device management (MDM) software. MDM software can lock and remove data from a device remotely if it’s lost or stolen.
Develop a contingency plan. You need a plan of action should an incident occur. It should include who to notify and how to remediate any weaknesses that allowed the crime to happen.
Maintain adequate insurance. Review your current insurance coverage to help ensure it protects against financial losses associated with physical and cybersecurity breaches. Some insurers offer policies that combine coverage for physical and cybersecurity risks.
Engage security professionals. Evaluating the effectiveness of your defenses can be a time-consuming and demanding process. Think about hiring a professional to scrutinize your physical environment and cyber defenses.
Simple solutions
It may seem obvious, yet many businesses neglect to address physical and digital security risks. Fortunately, simple and cost-effective solutions are available to help you safeguard all of your company’s assets. Contact us for help.
© 2024
Since its launch in 2021, Windows 11 has been continuously updated, bringing new features and improvements to make your life easier. But while big announcements like the AI assistant Copilot and expanded hardware support grab headlines, some lesser-known features deserve your attention, too. These hidden gems can make your Windows 11 experience quicker and easier, helping you stay productive and organized.
Focus Mode
Picture this: You’re deep into an important project, and suddenly, notifications start popping up – emails, instant messages, reminders. It’s hard to maintain focus with all these interruptions. Focus mode comes to the rescue by silencing them. To activate it, click the bell icon at the bottom right of your screen and select “Focus” from the menu. This will give you a 20-minute period with no interruptions, which you can pause anytime. It’s your digital “Do Not Disturb” sign.
Live Captions
Imagine you’re in a noisy office, or maybe you have some difficulty hearing. Understanding audio and video files can be challenging. Windows 11 has built-in live captioning that automatically generates captions for your content. You can activate it from the Accessibility settings (go to Settings > Accessibility > Captions) or by pressing Windows Key + Ctrl + L. The first time you use it, you must agree to Microsoft’s voice processing terms and download a speech pack. After that, captions will appear at the top of your screen, making it easier to follow along with any audio or video.
Voice Typing
If you find typing tedious, you’ll love Voice typing. This lets you dictate text instead of typing it. To start, press Windows Key + H. Make sure your microphone is connected (your webcam mic works fine). Click the mic button that appears, and you’re ready to go. You can even set it up to automatically punctuate your sentences. Voice commands like “stop listening” or “ignore that” help you control the flow of dictation. It’s a real time-saver for writing emails or documents.
Start Menu Features
Start menu folders are a game-changer if you want a tidy and efficient desktop. To create a folder, right-click an app and select “Pin to start.” Then drag another app over it, and they’ll combine into a folder. You can rename the folder and move it to the top of your Start menu for quick access to your most-used apps. It’s a simple way to keep things organized and within reach.
Snapping Bar
If you’re a multitasker, this feature is a lifesaver. It lets you snap windows into various layouts on your screen. Drag a window to the top of the screen, and layout options will appear. You can place windows in different positions, making the most of your screen space. You can also use the Windows key + arrow keys to snap windows into place. If you don’t see the snapping options, turn them on in Settings > System > Multi-tasking.
These features might not make headlines, but they can enhance your Windows 11 experience. Try them out and see how much time you can save.
Information used in this article was provided by our partners at MSP Marketing Edge.
I’m overwhelmed by the number of websites asking for location, notification, camera, and microphone access. Can I switch them off?
In the latest Edge browser in Windows, you can manage your privacy by going to a site, clicking the lock icon next to the website link, and selecting ‘Site permissions.’
Switching from window to window is a real pain when I’m busy. Is there an easier way?
Try split screen. Hover over the Maximize button of a window and choose Snap Layouts. This is only available on Windows 11, though. If you need help upgrading, get in touch.
Should I upgrade to Windows 11 or wait for Windows 12?
At the time of writing, there’s no release date set for Windows 12. However, we do know that support for Windows 10 will end next year, so upgrading to Windows 11 is a good idea.
Information used in this article was provided by our partners at MSP Marketing Edge.
In today’s fast-paced digital world, businesses rely heavily on technology to drive productivity, enhance communication, and streamline operations. However, with this increased dependency on technology comes a set of common IT problems that can disrupt business operations and affect overall performance. Understanding these issues and learning how to deal with them effectively is crucial for any business aiming to maintain a competitive edge. Here are some of the most common IT problems businesses face and strategies to address them:
1. Cybersecurity Threats
Problem: Cybersecurity threats, including malware, ransomware, phishing attacks, and data breaches, are among the most significant IT challenges for businesses of all sizes.
Solution: Implement a comprehensive cybersecurity strategy that includes regular software updates, strong password policies, employee training on recognizing phishing attempts, and investing in advanced security solutions such as firewalls, antivirus software, and intrusion detection systems. Conduct regular security audits and vulnerability assessments to identify and address potential weaknesses.
2. Data Loss and Recovery
Problem: Data loss due to hardware failures, accidental deletion, or cyberattacks can lead to significant operational disruptions and financial losses.
Solution: Develop a robust data backup and disaster recovery plan. This should include regular backups of all critical data, both on-site and off-site, and ensure that backups are tested periodically. Invest in cloud storage solutions for secure and scalable backup options and create a clear recovery procedure to minimize downtime in the event of data loss.
3. Network Downtime
Problem: Network downtime can slow business operations, leading to lost productivity, missed opportunities, and customer dissatisfaction.
Solution: Ensure that your network infrastructure is reliable and regularly maintained. Implement redundant systems and failover mechanisms to minimize downtime. Periodically monitor network performance and address issues proactively. Investing in high-quality networking equipment and working with a reliable internet service provider (ISP) can also help reduce the likelihood of network failures.
4. Outdated Technology
Problem: Using outdated hardware and software can lead to compatibility issues, security vulnerabilities, and decreased efficiency.
Solution: Establish a regular update and upgrade schedule for all technology assets. Conduct periodic assessments to identify outdated equipment and software and plan for timely replacements or upgrades. Consider leveraging cloud-based solutions to keep your technology infrastructure current without the need for significant capital investment.
5. Insufficient IT Support
Problem: Many businesses struggle with insufficient IT support, which leads to slow technical issue resolution and prolonged downtime.
Solution: Invest in a dedicated IT support team or partner with a managed service provider (MSP) to ensure 24/7 support. An MSP can provide proactive monitoring, regular maintenance, and quick response to technical issues, allowing your internal team to focus on core business activities. Establish clear communication channels and service level agreements (SLAs) with your IT support provider to ensure prompt and effective support.
6. Software Integration Issues
Problem: Integrating various software applications can be challenging, leading to data silos, inefficiencies, and increased operational costs.
Solution: Choose software solutions designed for seamless integration and compatibility. When necessary, work with IT professionals to develop custom integration solutions. Regularly review and optimize your software ecosystem to ensure that all applications work together harmoniously and that data flows smoothly between systems.
7. Compliance and Regulatory Challenges
Problem: Navigating complex regulatory requirements and ensuring compliance with industry standards can be daunting and time-consuming.
Solution: Stay informed about relevant regulations and compliance requirements in your industry. Implement policies and procedures to ensure adherence to these standards. Consider working with compliance professionals or consultants to audit your practices and make necessary adjustments regularly. Use technology solutions that offer built-in compliance features to simplify the process.
A Dedicated IT Support Partner Can Help
Businesses can minimize disruptions and maximize productivity by addressing common IT problems proactively and implementing robust solutions. Partnering with a dedicated IT service provider like Yeo & Yeo Technology can make a significant difference. Yeo & Yeo Technology offers customized IT support services tailored to your business needs, ensuring you have the right solutions to tackle any IT challenges. With our knowledge, proactive monitoring, and reliable support, you can focus on growing your business while we take care of your technology needs, providing peace of mind and a strong foundation for success.
In today’s technology-driven world, businesses of all sizes rely heavily on IT support to maintain smooth operations and ensure security. However, the cost of IT support can vary widely, influenced by several factors. Understanding these factors and implementing cost-control strategies can help businesses manage their IT expenses effectively.
Factors Influencing IT Support Costs
1. Scope of IT Support
-
- Range of Services: The broader the range of services required, the higher the cost. Basic support might include troubleshooting and software updates, while more extensive services encompass network management, cybersecurity, and data recovery.
- Complexity of Systems: Businesses with complex IT infrastructures, including multiple servers, cloud services, and many endpoints, will incur higher costs.
Cost-Control Strategy: Clearly define the scope of required services. Opt for modular service packages that allow you to pay only for what you need. Regularly review and adjust your IT support needs to avoid paying for unnecessary services.
2. Level of Support
-
- Reactive vs. Proactive: Reactive support, where services are provided as issues arise, tends to be less expensive than proactive support, which involves continuous monitoring and maintenance.
Cost-Control Strategy: Implement proactive measures to reduce the frequency of emergencies and leverage automation tools to monitor systems.
3. Location and Size of Business
-
- Business Size: Larger businesses with more employees and more extensive IT infrastructure will naturally incur higher costs.
Cost-Control Strategy: For larger businesses, negotiate volume discounts and long-term contracts to reduce per-user costs.
4. Project Complexity
-
- Specializations Required: Complex projects that require specialization or skilled expertise often cost more than routine projects.
Cost-Control Strategy: Invest in training for in-house teams or seek specialized providers.
Comparing IT Support Options
1. Managed Service Providers (MSPs)
-
- Cost: Generally involves a fixed monthly fee, which can range from $100 to $250 per user, depending on the scope and level of support.
- Advantages: Predictable costs, comprehensive support, access to a team of professionals, and proactive maintenance.
Cost-Control Strategy: Select an MSP with a flexible pricing model that allows scalability as your business grows. Regularly review service levels to ensure they align with your needs.
2. One-Time Service
-
- Cost: Charges can range from $125 to $250 per hour for on-demand support, depending on the complexity of the issue.
- Advantages: Suitable for businesses with minimal IT needs or those that only require occasional support.
Cost-Control Strategy: Establish a relationship with a reliable service provider who offers competitive rates for repeat customers. Invest in training staff to handle basic issues internally to reduce dependency on one-time services.
3. Self-Managed/In-House Support
-
- Cost: Includes salaries of IT staff, benefits, training, and equipment, which can be substantial. For instance, an in-house IT manager’s salary can range from $80,000 to $120,000 annually.
- Advantages: Full control over IT operations, immediate response to issues, and a team that understands the business’s specific needs.
Cost-Control Strategy: Implement efficient IT management practices and continuous training to maximize the productivity of in-house staff. Use automation tools to handle routine tasks, reducing the workload on your IT team.
Yeo & Yeo Technology: Customized IT Support Solutions
At Yeo & Yeo Technology, we understand that every business has unique IT support needs. Our comprehensive range of services is designed to provide customized solutions that align with your specific requirements. Whether you need a managed service provider, occasional support, or assistance with in-house IT management, we have the expertise and flexibility to help your business thrive. Partner with us to leverage our broad range of services and find the perfect solution to enhance your IT infrastructure and support your growth.
Yeo & Yeo Technology partner KnowBe4 recently established August 6 as National Social Engineering Day. This initiative aims to highlight the pervasive threat of social engineering in cyberattacks and equip individuals and organizations with the knowledge to combat these tactics effectively.
Understanding Social Engineering Cyberattacks
Social engineering is a manipulation technique cybercriminals use to deceive individuals into divulging confidential information or granting access to systems. This attack exploits human psychology rather than technical vulnerabilities, making it particularly effective. Cybercriminals often employ tactics such as creating a sense of urgency or exploiting trust to achieve their goals.
Social engineering typically involves:
- Human Element: Unlike technical defenses, human behavior is unpredictable and can be easily manipulated. Attackers exploit natural human tendencies such as trust, fear, and the desire to help others.
- Sophisticated Tactics: Cybercriminals often conduct extensive research to craft convincing scenarios, such as business email compromise (BEC) attacks. These attacks involve impersonating trusted contacts to deceive victims into transferring funds or sharing sensitive information.
- Wide Reach: Social engineering is involved in an estimated 98% of cyberattacks, causing significant financial and operational disruptions.
Preventing Social Engineering Attacks
To defend against social engineering, organizations, and individuals must adopt a proactive approach:
- Security Awareness Training: Regular training sessions can educate employees about recognizing and responding to social engineering tactics. This training should cover various attack vectors, including phishing, spear phishing, and vishing.
- Vigilance and Verification: Encourage employees to verify requests for sensitive information or financial transactions through independent channels, such as direct phone calls to known contacts.
- Use of Security Solutions: Implement robust security solutions to detect and mitigate potential threats before they reach end-users. However, the human element remains the last line of defense, emphasizing the importance of awareness and training.
As cyber threats evolve, organizations must prioritize security awareness to protect their assets and data. Yeo & Yeo Technology offers comprehensive security awareness training designed to empower your team with the skills to identify and thwart social engineering attacks. Investing in such training can transform your workforce from a potential vulnerability into a formidable defense. Contact Yeo & Yeo Technology today to learn more about our security solutions and how we can help safeguard your organization.
More and more businesses are making smart decisions to be proactive and invest in their cybersecurity defenses. This is fantastic news, especially since stats show that about half of SMBs still have no cybersecurity measures at all. If your business falls into that category, it’s time to change.
Cybersecurity might sound complex, but it starts with a few simple steps. Let’s talk about some basics you can put in place right away.
- First, think about encryption and multi-factor authentication (MFA). Encryption is like putting your data in a secure vault. It ensures that even if someone intercepts your information, they can’t read it without the encryption key. MFA adds an extra layer of security by requiring you to verify your identity using a second device, like your phone, whenever you log in. It’s like needing two keys to open a lock instead of just one.
- Another easy step is using a password manager. These generate long, random passwords for every account and remember them for you. Password managers make life easier and your business more secure in one package.
- Advanced monitoring tools are another great way to protect your business. They’re a little like security cameras for your digital space, always on the lookout for anything suspicious. These tools help detect unusual activity in your systems, alerting you if something’s wrong.
- And let’s not forget about protecting your business from phishing scams. These are attempts by criminals to trick you into giving away personal information by pretending to be someone you trust, like a supplier or a bank. Educating your team on how to spot these scams is crucial. If something feels off, it probably is.
Why is investing in cybersecurity so important?
- It protects your data
- Avoids financial loss
- And builds trust with your customers and partners
Your business data is valuable; protecting it means safeguarding your business’s operations and reputation. Cyberattacks can be costly, not just in terms of money but also time and resources. Prevention is almost always cheaper than dealing with the aftermath of a breach. Plus, showing that you take security seriously helps build trust with your customers and partners. They need to know that their information is safe with you.
Investing in cybersecurity doesn’t have to be daunting. Yeo & Yeo Technology is here to help. Whether you need advice on getting started or want a comprehensive security plan, get in touch.
Information used in this article was provided by our partners at MSP Marketing Edge.
Which is the best browser to use?
It comes down to personal preference, but check your chosen browser is secure, has tools that work for you, and can be as private as you need it to be.
What’s the difference between 2FA and MFA?
2FA (two-factor authentication) requires two types of authentication: a password and a one-time code. MFA (multi-factor authentication) requires at least two or more types of authentication.
Which is best, 2FA or MFA?
The answer depends on how your business works and what you’re securing. Ideally, you’d use the method that offers the highest security standards yet requires the least effort. We can help you figure this out – contact us.
Information used in this article was provided by our partners at MSP Marketing Edge.
QR codes offer a convenient way to access information, make payments, and interact with services. However, this convenience comes with a growing risk: cyberattacks. As QR code usage has surged, so too have the number of cyberattacks exploiting this technology. A 2023 study of 38 organizations across nine industries and 125 countries revealed that 22% of phishing attacks used QR codes to deliver malicious payloads.
What to Watch For
Cybercriminals often tamper with digital and physical QR codes to replace legitimate ones with malicious ones. Here are some common tactics to be aware of:
- Phishing Sites: Scanning a malicious QR code can direct you to a phishing site that prompts you to enter sensitive information, such as login credentials or financial details.
- Malware Downloads: Some QR codes can initiate malware downloads onto your device, compromising your data and security.
- Fake Payment Portals: Scammers may use QR codes to create fake payment portals, tricking you into transferring money to them instead of the intended recipient.
Protecting Yourself
To safeguard against QR code cyberattacks, consider the following precautions:
- Verify the Source: Only scan QR codes from trusted sources. Be cautious of codes found in public places or unsolicited messages.
- Use a QR Scanner with Security Features: Some QR scanner apps offer security features that can detect malicious codes before they are opened.
- Check the URL: Before entering any information, check the URL that the QR code directs you to. Ensure it is legitimate and secure (look for “https” and a padlock icon).
- Update Your Device: Keep your device’s operating system and security software up to date to protect against the latest threats.
The Role of Cybersecurity Awareness Training
One of the most effective ways to combat QR code cyberattacks is through comprehensive cybersecurity awareness training. Educating employees about the risks associated with QR codes and how to recognize potential threats can significantly reduce the likelihood of falling victim to these attacks. Training should cover:
- Identifying Suspicious QR Codes: Teaching employees to spot potentially malicious QR codes.
- Safe Scanning Practices: Encouraging the use of secure QR scanner apps and verifying the legitimacy of URLs.
- Reporting Procedures: Establishing clear protocols for reporting suspected cyber threats.
By fostering a culture of cybersecurity awareness, organizations can empower their employees to act as the first line of defense against QR code cyberattacks.
At Yeo & Yeo Technology, we offer comprehensive cybersecurity awareness training programs tailored to your organization’s needs. By partnering with YYTECH, you can create a robust security culture within your organization, protecting your valuable data and maintaining trust with your clients. Stay vigilant, stay informed, and let YYTECH help you stay secure.
The loss or theft of a work device can have serious implications, from data breaches to financial loss and compromised customer trust. Here’s what you should do when devices go missing:
First and foremost, create an environment where employees feel comfortable reporting a lost or stolen device immediately. Employees should know that the sooner they inform the company, the better. Emphasize that there will be no blame or punishment – what matters most is safeguarding the data.
Ensure that all work-issued devices have remote wiping capabilities. This is your first line of defense. When an employee reports their laptop missing, your IT team should be able to wipe the device remotely, erasing all data to prevent unauthorized access. However, keep in mind that the laptop or desktop needs to be online for remote wiping to work. A better solution is to use hard drive encryption, such as BitLocker from Microsoft, which provides an additional layer of security by encrypting the data on the device, ensuring it remains inaccessible even if the device is offline.
Before a device is lost, proactive measures can make a world of difference. Make sure all company devices are encrypted. Encryption converts data into a code to prevent unauthorized access. Even if someone gets hold of an employee’s lost laptop, encrypted data remains inaccessible without the proper decryption key. Most modern operating systems offer robust encryption options.
Consistently enforce strong password policies. Every employee’s laptop should have a complex password and, ideally, two-factor authentication (2FA). This adds an extra layer of security, making it harder for anyone to access the data if they bypass the initial password protection.
Regular training is vital. Employees should understand the importance of device security and the steps to take if a device is lost or stolen. Conduct workshops and send reminders about security protocols. The more informed employees are, the quicker and more effectively they can respond to the loss.
Why are these steps so crucial?
The consequences can be severe if an employee’s laptop falls into the wrong hands. Unauthorized access to customer files can lead to identity theft and loss of client trust. Exposure of financial data could result in significant loss and legal consequences. Proprietary information could be stolen and sold. It’s a nightmare.
By implementing these strategies, you can sleep easier knowing that your company’s data remains secure, even if a device goes missing. It will become a minor annoyance, not a disaster.
We can help you create and implement a plan for this kind of scenario. Get in touch.
Information used in this article was provided by our partners at MSP Marketing Edge.
Cybercrime is on the rise, affecting businesses and individuals. Cybercriminals operate without discrimination, targeting victims worldwide 24/7. Despite advancements in digital security, attackers have shifted their focus to exploit human vulnerabilities within increasingly fortified organizations.
With the integration of artificial intelligence (AI) into technology, cybersecurity vigilance is more vital than ever. AI systems can swiftly analyze vast datasets and detect patterns beyond human capacity. However, this advancement presents a dual challenge. While enhancing efficiency, it equips hackers with sophisticated tools to identify and exploit vulnerabilities, accelerating the pace and scale of cyberattacks.
As AI-driven cyber threats evolve, security awareness programs must urgently adapt, with a particular emphasis on managing human risks. According to KnowBe4’s 2024 Phishing by Industry Benchmarking Report, 34.3% of untrained end users will fail a phishing test. After 90 days of security awareness training, the number drops to 18.9%. After one year, only 4.6% of users will fail. Of all industries tested, healthcare and pharmaceuticals had the worst baseline fail rate in both the small and large business categories.
Organizations must prioritize addressing the human element in cybersecurity. Implementing a modern security awareness approach involving comprehensive and ongoing education, testing, and communication can empower employees to serve as the primary line of defense.
Key Cybersecurity Recommendations for Businesses:
- Foster a resilient security culture where employees understand their role in safeguarding the organization against cyber threats.
- Increase the frequency of security awareness training while optimizing time efficiency to drive lasting behavior change.
- Implement regular simulated phishing campaigns to enhance employees’ ability to detect and thwart phishing attempts.
- Collaborate with security awareness professionals to design engaging and effective training content tailored to behavioral changes.
Many organizations perceive training as a mere obligation rather than a strategic initiative to cultivate a security-conscious culture. However, establishing such a culture requires a sustained and comprehensive approach, with continuous efforts to reshape behaviors and instill secure practices. This journey has no endpoint; only through relentless commitment can organizations mitigate cybersecurity risks effectively.
Information used in this article was provided by our partners at KnowBe4.
Artificial intelligence (AI) has become more than just a buzzword; it’s a transformative force reshaping businesses’ operations. From streamlining workflows to enhancing decision-making processes, AI technologies are increasingly integrated into various aspects of the workplace. However, as with any powerful tool, there are both opportunities and risks associated with its adoption. Businesses must tread carefully to maximize the benefits while safeguarding against potential pitfalls for themselves and their employees.
The Uses of AI in the Workplace
According to ISACA, in a poll of 3,270 digital trust professionals, 35% say they use AI to increase productivity, and 33% use it to automate repetitive tasks and create written content. AI offers a myriad of opportunities for businesses to optimize operations and drive growth:
- Automation: AI’s most significant advantage is its ability to automate repetitive and mundane tasks, allowing employees to focus on more creative and strategic endeavors. From data entry to customer service inquiries, AI-powered bots and algorithms can handle routine tasks efficiently, improving productivity and reducing human error.
- Data Analysis: With the vast amount of data businesses generate today, AI analyzes complex datasets to extract valuable insights. From market trends to customer preferences, AI algorithms can uncover patterns and trends that human analysts might overlook, enabling data-driven decision-making.
- Personalization: AI enables businesses to deliver personalized experiences to customers and employees. By analyzing individual preferences and behavior, AI algorithms can tailor products, services, and even employee training programs to meet specific needs, enhancing satisfaction and loyalty.
- Predictive Maintenance: AI-powered predictive maintenance systems can anticipate equipment failures before they occur in industries like manufacturing and logistics. By monitoring machine performance and analyzing historical data, businesses can minimize downtime, reduce maintenance costs, and prolong the lifespan of assets.
The Risks of AI in the Workplace
In the same poll, ISACA found that 70% of organizations use AI, and 60% use generative AI. However, only 15% have AI policies, and 40% don’t offer any AI training. Despite its transformative potential, AI adoption in the workplace is not without its risks:
- Cybersecurity Threats: As AI adoption grows, cybercriminals may exploit AI for large-scale attacks. Malicious use of AI could overwhelm businesses and disrupt operations.
- Data Manipulation: Threat actors may target workforce-related data, compromising its accuracy and credibility. Manipulating AI models or data storage poses a significant risk.
- Data Privacy: Employees using generative AI platforms at work can inadvertently leak sensitive information or compromise systems. Some companies restrict or ban AI to mitigate risks.
Protecting Businesses and Employees
To navigate the complexities of AI in the workplace and ensure a positive outcome for both businesses and employees, several strategies can be employed:
- Invest in Education and Training: It is crucial to empower employees with the skills and knowledge needed to work alongside AI technologies. Implementing comprehensive training programs and fostering a culture of continuous learning can help employees adapt to technological changes.
- Enhance Data Governance: Establishing robust data governance frameworks is essential for protecting data privacy and security in the age of AI. This includes implementing encryption, anonymization, access controls, and complying with relevant regulations.
- Ongoing Oversight: Monitor AI usage internally to detect any misuse. Regular assessments help align AI practices with ethical and legal standards.
AI holds immense promise for transforming the workplace, offering unprecedented automation, data analysis, and personalization opportunities. However, realizing these benefits requires careful consideration of the associated risks and challenges. By investing in education and training, enhancing data governance, and continuously monitoring AI use, businesses can harness AI’s full potential while safeguarding their employees’ well-being and maintaining trust with customers and stakeholders.